Securing a Whole Microsoft Teams Environment
In most organizations, end-users must work together to perform specific tasks, work on projects or collaborate. Microsoft 365 provides multiple tools that facilitate all types of collaboration. The most recent application to use is Microsoft Teams, which allows people to work together around these types of common goals, decisions, or projects.
Microsoft Teams is a front-end to multiple services within Microsoft 365. It provides chat, voice, meetings, storage, document collaboration capabilities, and other underlying management controls, such as a security group for securing permissions and access. Combining these multiple services and applications into a single-entry point is fantastic, but managing them can be complicated. As with most services within Microsoft 365, though they provide excellent capabilities, they are often not optimized for specific organizational needs and overall management. You may also find that complete lifecycle management of certain features does not meet the general business needs.
Core concerns with Microsoft Teams
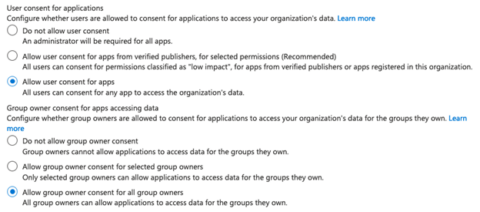
Out-of-the-box Microsoft Teams is simple and easy to use for all users. End-users can create Teams as and when needed, often without the need for approval or understanding of what gets built. With all the components formed as part of Microsoft Teams, many organizations often find hundreds of Teams created, which means that hundreds of SharePoint Online site collections get created. Users can also store content in both the primary and secondary site collections that map to private channels. Remember that content could also reside within OneDrive for Business and other applications such as Planner, which integrates into the Teams. The most common problems are large amounts of Teams content and the associated site sprawl. Another less-discussed concern is connected apps that may also contain data. By default, end-users can grant access to connected apps to personal data and stored information such as documents and files. Too often, organizations do not control or limit this capability allowing unwanted dissemination of content.
To manage and govern Microsoft Teams successfully and meet all organizational security requirements and any legal requirements or classification, you need governance. However, many things can impact Microsoft Teams from a management and governance perspective, which are unrelated to the team and site collection sprawl that often happens. A few of these are:
- Team naming convention
- External sharing configuration
- Security and access control
- Team privacy
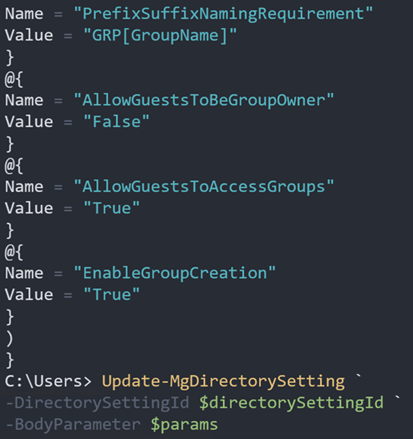
1. Team naming convention
An end-user can name a team anything by default. The name associated with the team then flows to the Microsoft 365 Group, SharePoint site collection, and supporting services. It can often cause problems when multiple components of the Teams contain the same name or may not make any sense as they don’t follow a standard naming convention.
2. External sharing configuration
By default, SharePoint Online, a supporting Teams service, allows for external sharing to anyone. When a team gets created, unless this control is adjusted, as soon as end-users add content through Teams, they could easily share content with anyone, violating existing security policies for external sharing.
3. Security and access control
Microsoft Teams uses an Azure Active Directory group for managing members of the team. The group has the same name as the created team and allows adding users directly to the group or through the application. The same is true for permissions within the supporting services such as SharePoint Online, which hides the standard security management in favor of the Teams interface. Most Teams end up with more users than required as end-users can often manage the members themselves, providing access to users who do not need it.
4. Team privacy
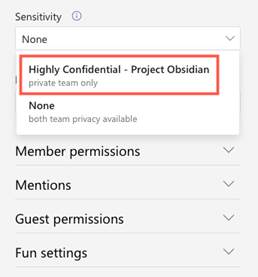
Sometimes Teams need extra security due to the sensitivity of members, content, or privacy requirements. Teams natively support classification to help control the dissemination of content to both internal and external users. Many organizations, however, do not realize these capabilities are not within Teams but part of the overall Microsoft Purview security and compliance feature set. Enabling this feature within Teams requires specific configurations which are not part of Microsoft Teams.
Management and Governance
Microsoft Teams is not an application that should be left alone. Organizations need to plan and prepare for a Microsoft Teams deployment and then the overall management and governance of the created Teams and corresponding services.
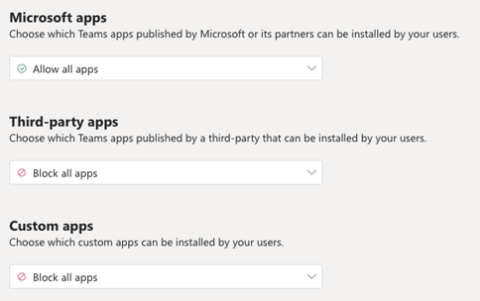
You can secure and govern Microsoft Teams using either the administration centers, PowerShell, or Microsoft Graph. The main problem is that you need to manage multiple services, not just Teams. To manage, you often need to use combinations of the following:
- Microsoft 365 Administration Center
- Teams Administration Center
- Azure Active Directory Portal
- SharePoint Administration Center
- Security Center
- Compliance Center
You can also utilize scripting within PowerShell using combinations of the following modules:
- Azure Active Directory (AzureAD)
- Azure Active Directory Preview (AzureADPreview)
- Microsoft Online Services (MsolOnline)
- Microsoft Teams (MicrosoftTeams)
- Exchange Online (ExchangeOnlineManagement)
- SharePoint Online (Microsoft.Online.SharePoint.PowerShell)
The difficulty is identifying the administration center or PowerShell module to use. Sometimes there is no way to perform a specific configuration, and you may even need to call the Microsoft Graph directly. Microsoft has also provided you with the Patterns and Practices PowerShell modules that focus on SharePoint Online and Microsoft Teams to help with the administration.
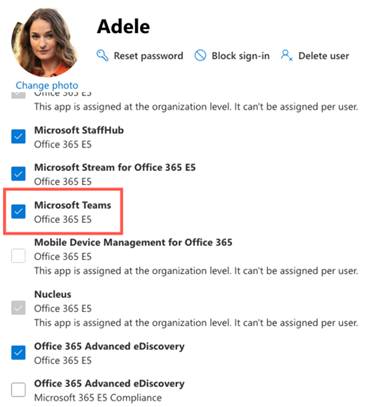
For example, for end-users to use Microsoft Teams, they must have a license assigned to them. You cannot complete this within the Microsoft Teams administration center or the Team PowerShell module. To assign licenses, you must use either the Azure Active Directory Portal, Microsoft 365 Administration Center, or PowerShell using either the Azure Active Directory (AzureAD) or Microsoft Online Services (MsolOnline) modules.
Another example could be assigning a classification to a team to control the dissemination of content to external users, which requires work within Microsoft Purview via the Compliance Center and then accessing the Team configuration within the Microsoft Team’s Administration Center.
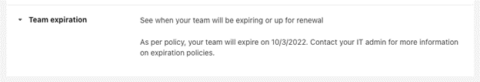
Suppose you need to provide lifecycle management of Microsoft Teams. In that case, this function resides within the Microsoft Team’s Administration Center and is as simple as adding an expiration policy that offers a renew Team option. However, this may not work for advanced use cases, and you may need to use other features within the Microsoft Purview Compliance Center to meet the business requirements.
Though you can script much of the configuration, you still need to load multiple PowerShell modules, make numerous connections to the services, and script the creation and deployment.
Regardless of which approach you choose, it still requires multiple steps and tasks to manage Team’s configuration, security, and controls.
For most organizations with standard requirements, the out-of-the-box tools will suffice and allow proper management and governing of Microsoft Teams. However, this changes over time, especially as the number of Teams, the dependency on them, and the maturity of using cloud services changes. As organizational usage increases within Teams, so does the complexity of management and controls. IT Teams require specific skills for securing Teams and supporting Microsoft 365 services. Many organizations do not have the necessary skills in-house and need to invest in training or hiring individuals who have the required skills. Even with the right skills, securing Teams becomes a time-consuming task due to excessive usage.
IT and Support Expectations
Securing and Governing Microsoft Teams falls on the shoulders of the IT and Support departments and Teams within most organizations. The most common approach allows end-users to create what they need when they need it and provides support using a ticket-based method. The problem with this approach is that by the time an end-user potentially has an issue affecting Microsoft Teams, the created Team is mission-critical, and adjusting becomes complicated. It can be very complex to undo poorly implemented security, lock down a created team that is wide-open, change a team to use a different Template, copy a team, and even report on the Team’s usage and activity.
The expectation is that IT and Support Teams can adjust as needed using standard tooling and efficiently when it is much more complicated. The key to successfully securing and governing Microsoft Teams is using out-of-the-box capabilities in planning everything upfront, implementing, and being consistent with the tooling. Organizations must also remember some features don’t currently exist within Microsoft Teams. The most significant risk is the number of Teams and corresponding SharePoint site collections created, which provide external sharing capabilities. It often becomes hard for IT to know which SharePoint site collections are Teams connected and which are not. It can also become very complicated to control external content sharing when end-users create Teams as they need and share without restrictions.
Conclusion
Overall, Microsoft Teams provides excellent tooling to meet nearly all securing and governing team requirements. Though you may need to use multiple administration centers, PowerShell modules, or other services, you can do it. The tools may not be the most elegant and cohesive, but they get the job done, even if it takes longer and is more complicated to implement. Being successful, more innovative, faster, and securing Teams requires dedicated time, resources, and a solid competency in Microsoft 365 Technologies and tools. You will also find that you are constantly jumping between various services and tools to get the job done.
Written by Liam Cleary, Microsoft MVP and MCT, CEO, and owner at SharePlicity.
About the Author – Liam Cleary

Liam began his career as a trainer of all things computer-related. He quickly realized that programming, breaking, and hacking were much more fun. Liam spent the next few years working within core infrastructure and security services. He is the founder and owner of SharePlicity, a consulting company that focuses on Microsoft 365 and Azure technology. His role within SharePlicity is to help organizations implement Microsoft 365 and Azure technology to enhance internal and external collaboration, document and records management, automate business processes, and implement security controls and protection.
Emily Houssier
Regional Marketing Manager
Comme dans "Emily in Paris", Emily s'appelle Emily et vit à Paris. La comparaison s’arrête là. Emily poursuit une mission personnelle : rendre la Digital Workplace un peu moins… digitale. Pour elle, le marketing ne se résume pas au pipeline et à la performance ; il s’agit avant tout d’aider les équipes à réellement se parler, à s’aligner autour d’une histoire commune et à construire des environnements de travail que l’on a sincèrement envie d’utiliser.